Open Vulnerability Database
Query 150+ sources across CVEs, exploits, advisories, and malware feeds.
One API. Every identifier format. Always current.
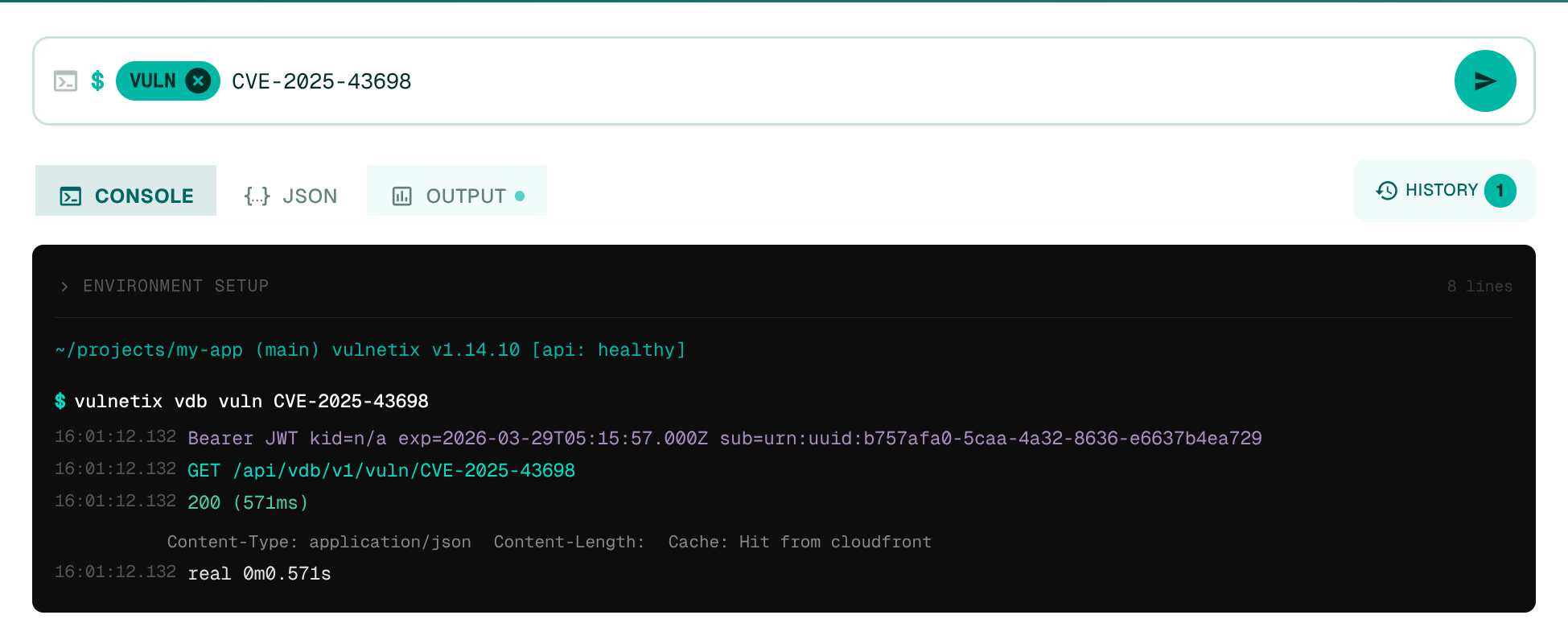
Built for Your Agents, Terminal, and Your CI
Search across all identifier formats — CVE, GHSA, PYSEC, RUSTSEC, and more. Get exploit data, fix advisories, scoring metrics, and remediation plans from a single query. JSON output, piping, scripting — the VDB fits your existing toolchain, not the other way around.
- CLI
- REST API
- JSON output
- CI/CD pipelines
- 78+ ID formats
- OpenAPI
Intelligence Sources
Aggregated, normalised, and enriched from 150+ authoritative sources. Every record is tagged with its origin, linked to upstream advisories, and queryable by any identifier.
Vulnerability Authorities
23 sourcesNormalised records from every major vulnerability database and numbering authority worldwide.
Government & National Cyber Defence
16 sourcesAdvisories from 14+ national CERTs and government cybersecurity agencies.
Vendor & Product Security
24 sourcesConsolidated vendor intelligence with structured affected-product data.
Supply Chain & Malware Detection
9 sourcesMalicious package detection across typosquatting, dependency confusion, and backdoored code.
Exploit Intelligence
21 sourcesExploit availability, PoC code, framework modules, and weaponisation status.
Threat Observation & Research
9 sourcesLive exploitation signals from honeypots, scanning infrastructure, and research communities.
Ecosystem & Patch Intelligence
47 sourcesPatch availability across 30+ distributions and ecosystems with version-specific fix tracking.
VDB intelligence inside your AI agent
Works with 41+ Agents that support SKILLS.md — Claude Code, Cursor, Windsurf, and more. One install, zero context-switching.
Vulnerability Intelligence in your Coding Agent
The Vulnetix Claude Code plugin brings VDB queries directly into your development flow. Look up a CVE, check exploit status, or get remediation guidance without switching context. Works through the MCP server protocol — same endpoints, same data, zero context-switching.
- Works with 41+ agents that support SKILLS.md
- Claude Code, Cursor, Windsurf, and more
- Inline vuln lookups
- Exploit status checks
- Remediation guidance
- Fix version lookups
Security That Respects the Developer Flow
Not another fire drill. Not another ticket that says “critical” because a scanner said so. When a security engineer brings a vulnerability to a developer, it should be backed by data — exploit intelligence, EPSS probability, KEV status, SSVC prioritisation — not anxiety.
Drop-tools moments should be rare, researched, and respected. The VDB gives security teams the evidence to make that call with confidence, and developers the context to understand why this one actually matters.
- Exploit Prediction scoring
- Decision Tree prioritisation
- 3x Known Exploited Vulnerabilty databases
- Exploit weaponisation and real usage
- Fix/Patch analysis